Report
Consumer Technology Trends: What’s Changing in 2025?
Here are the trends dominating the consumer technology industry.
Get startedWhat’s changing in consumer technology? We’ve analyzed over 261 million online mentions so that you can tap into the latest tech trends.
From a boom in social media-fueled ecommerce to an influx of AI-infused products, brands in the consumer technology space are facing increasing pressure to innovate. Read on to discover how your brand can navigate these changing market expectations.
In this report, we’ll look at the broad state of online consumer tech conversations and cover the following five trends:
- Consumers have high expectations around AI ethics and personalization
- There's huge buzz around budget electronics
- Retro tech products are making a comeback
- Consumers are no longer prioritizing repairs
- Wearables are set to boom
Methodology
For this report, we used Brandwatch Consumer Research to analyze over 261 million online conversations around consumer technology from public social posts, blogs, forums, and review sites between 1 Jan 2022 and 1 Nov 2024. Social media benchmark data was pulled from Brandwatch Benchmark.
An overview of consumer tech conversations
There were over 79 million online mentions about consumer tech between January and October 2024. From Reddit forums discussing the best wearables to X threads debating the latest video game consoles, these online mentions can paint a clear picture of how tech brands can best serve their customers in 2025.
Let’s dive into where brands can find these conversations.
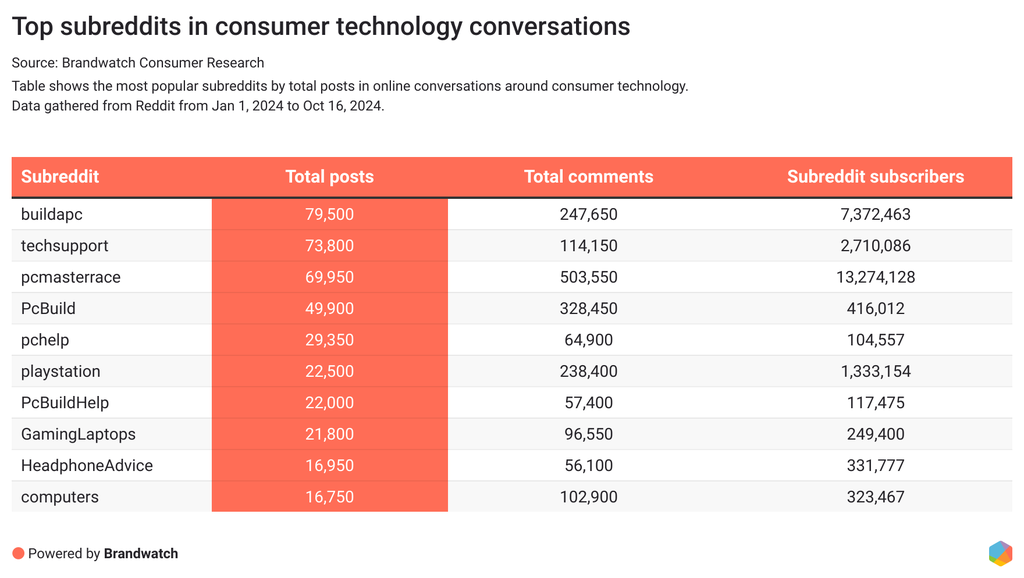
The top subreddits for consumer tech conversations
Conversations about tech dominate plenty of subreddits. With consumers keen to get authentic product feedback from real people, Reddit is a place where niche tech communities can thrive.
Here are the top subreddits in 2024 for conversations about consumer tech.
More general subreddits, such as r/computers and r/playstation, are go-to places for people to get tips and advice from the community. More specific subreddits are also popular, such as r/buildapc, which offer an opportunity for niches to thrive.
You may be surprised to see that the more ”niche” communities on this list are often more active than the “general” ones. For example, r/buildapc has many more posts, comments, and subscribers than the general r/computers subreddit.
Here are some of the most discussed topics in the top consumer tech subreddits:
- Computer building enthusiasts discussing PC builds, seeking compatibility advice, or exploring future-proofing options
- Queries on internet issues, data backup options, and software compatibility
- Upgrade considerations and product recommendations
- Gaming console experiences, challenges, and solutions
With 70% of these subreddits being dedicated to computers, brands in this space have a treasure trove of data to dig into to discover what’s making their customers tick.
The most used consumer tech emojis
By using language which your potential customers are using, you’re more likely to offer authentic, relatable captions and content in your marketing efforts. Emojis are an important part of that, and understanding their meanings will help you pick the right ones.
Let’s take a look at which emojis are trending in consumer tech conversations right now.
| Rank | Emoji | How the emoji is used in consumer tech conversations |
|---|---|---|
| 1 | 😭 | Used to express tech frustrations, emotional attachment to devices, and general everyday humor |
| 2 | 😂 | Appears alongside funny tech anecdotes or gadget experiences and mishaps |
| 3 | 🎮 | Used to share photos of stylish gaming set ups and stories of people's favorite games |
| 4 | 🔥 | Shared alongside excitement for new tech releases |
| 5 | 🚀 | Used to celebrate innovative gaming accessories, as well as exciting developments in the Web3 and general tech space |
| 6 | 🤣 | Appears alongside excitement over new purchases and humorous everyday tech-related stories |
| 7 | ❤️ | Shared to show appreciation for gadgets, as well as a passion for tech, devices, and games |
| 8 | 🌟 | Used in conversations about innovative tech gadgets and cutting-edge electronics |
Emojis can enhance your social media captions, advertising, and website copy. But if you’re stuck on which emojis to use, try utilizing the ones above to better connect with your audience.
Social media benchmarks for brands in consumer tech
With Benchmark, we’ve analyzed how some of the largest brands in computer software and electronics operate on social to define helpful benchmarks for brands in this industry.
Here are some interesting benchmarks for tech brands:
- On average, tech brands post 57 times per month on X and 22 times per month on Instagram.
- On average, tech brands post 20 times per month on YouTube, with an average video duration of over 5 minutes and an average like count of 166,557.
- The average tech brand’s Instagram post engagement rate is 9.01%.
These social media benchmarks can help brands in consumer technology understand how they are performing on social media compared to others in their industry.
Check out more helpful social media benchmarks for the technology industry here.
Consumers have high expectations around AI ethics and personalization
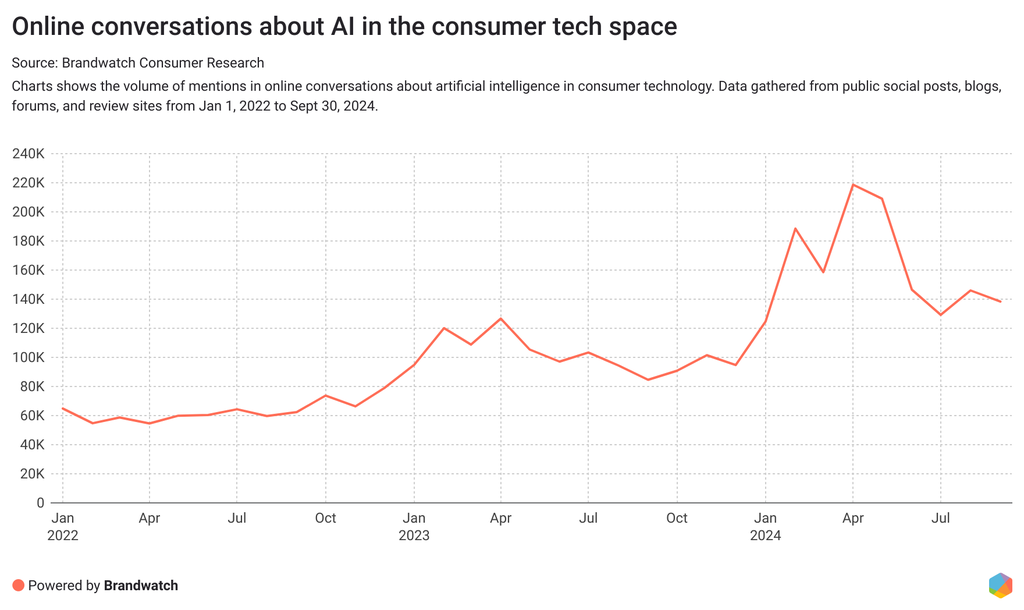
There were over 1.31 million online mentions about artificial intelligence among consumer technology conversations between January and October 2024.
From increased personalization in smart home devices to revolutionized gaming experiences, it's clear that AI is becoming a more familiar part of consumer tech products. But what do consumers really think? And how can brands stay on top of customer expectations? Let’s take a look.
We used Brandwatch Consumer Research to track mentions of artificial intelligence in consumer technology conversations between 2022 and 2024. Mentions saw a steep incline in the first few months of 2024, hitting a peak of 218k mentions in April.
Online conversations during this incline focused on a few key areas, including how AI is converging with gaming to improve player experiences, and the role of AI in smartphones, cameras, and smart home devices.
Mentions have declined since peaking in April but are still elevated compared to pre-2024 levels.
The rise and fall of mentions about artificial intelligence in consumer technology might allude to a change in customer expectations. With AI being integrated into day-to-day technology, consumers are getting used to having it at their fingertips. Let’s look at how AI is shaping the conversation around specific areas of consumer tech.
AI and smart home devices
Devices like smart thermostats, lighting, and security systems are becoming increasingly integrated with AI to improve convenience, security, and efficiency. Plus, by learning user habits, these devices can help to optimize energy usage and to automate daily routines.
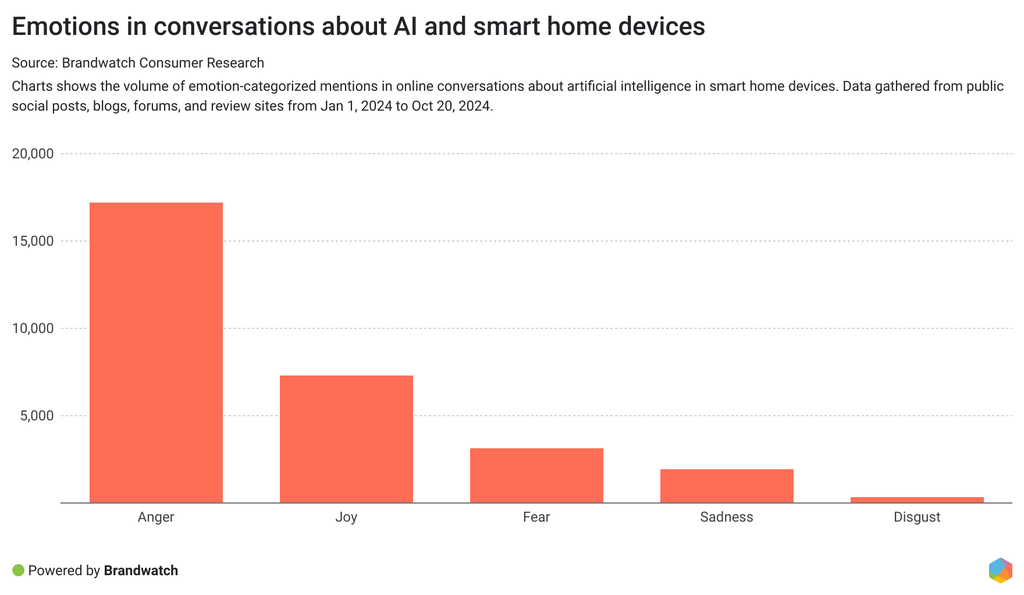
There were over 61k unique authors discussing the use of AI in smart home devices between January and October 2024. Digging into these user mentions can help us understand consumer expectations about integrating AI into this technology.
Looking at the emotional context of conversations, we find that people are frustrated. 57% of emotion-categorized mentions expressed anger.
While users appreciate the convenience that AI integrations offer, there are some key frustrations that appear in these online conversations. These include:
- Challenges when setting up and installing these devices
- Criticisms on device limitations and a lack of personalized responses
- Devices have difficulty understanding complex commands
- Requests for more seamless integrations to enhance user experiences
Many users are quick to shun AI assistants in online conversations. Some users don’t recognize the benefits, and some are worried about AI having too much of their personal information.
A common theme is frustration around generic or primitive AI assistants in smart home products. Essentially, some consumers would rather a product had no AI than ineffective AI.
Immediately disliking the stapled on AI assistant in every product. Unpredictable experience so I'd rather not bother. Feels like slop every time.
— Daniel (@growing_daniel) July 6, 2024
Companies should hold back on releasing AI in their products for the sake of it. Instead, invest in utilizing artificial intelligence in ways which meet growing consumer expectations.
With the market value of global smart home devices expected to reach $135 billion by 2025, brands in this space need to make sure they’re addressing customer frustrations head on to stand out in the market.
AI and gaming
With smarter NPCs (non-playable characters), adaptive difficulty levels, and improved personalization, AI is shaping the future of the gaming industry.
AI has been used in the background for game development for a while now. Whether it’s through procedural content generation (the creation of new game environments) or enhanced graphics thanks to AI-driven upscaling technology, developers aren’t strangers to leveraging artificial intelligence. However, from the consumer point of view, the concept of AI within gaming is relatively new. And it’s somewhat controversial.
The ethics of AI use is pressing in the gaming space. Consumers are quick to shun any use of AI which raises concerns about job displacement or creative ownership. In fact, using artificial intelligence in these ways can actively put people off your game.
Take the post below, for example. This voice actor–turned influencer has shared that they won’t be playing a game which uses AI voices. And with over 800k views, the post received a lot of support.
Heeeeeeeey I hate to be that guy, but it was brought to my attention. That Liar's Bar game, uses Ai voices.
— 🤖 CyYuVtuber 🤖 (@CyYuVtuber) October 16, 2024
So I won't be playing it, sorry. And if you're wondering where it says it, literally on their steam page. Unfortunately at the BOTTOM of it. pic.twitter.com/6ZhdA1IkYv
An interesting debate opened up in the replies to the post, with some understanding how low-budget game creators might resort to AI to save money. However, many agreed that this is still an unfair use of the tool when there are many affordable voice actor options available.
So, keeping the ethical debate of utilizing AI at the forefront of any game development process can help keep consumers engaged in the right way.
The future of gaming is woven in with AI advancements, and consumers are interested to see the ways this will improve their experiences.
There's a huge buzz around budget electronics
Budget ecommerce stores have had a boom this year as customers have found it easier than ever to get their hands on budget electronics.
With platforms like TikTok Shop, and even Temu, selling easily accessible, affordable tech devices, consumers are enjoying the opportunity to purchase handy home gadgets like self-heating mugs, mini projectors, wireless lamps, or other items they previously didn’t know they needed.
Often marketed as “must-have” products, these ecommerce stores make it much easier to make impulse purchases on tech products, too.
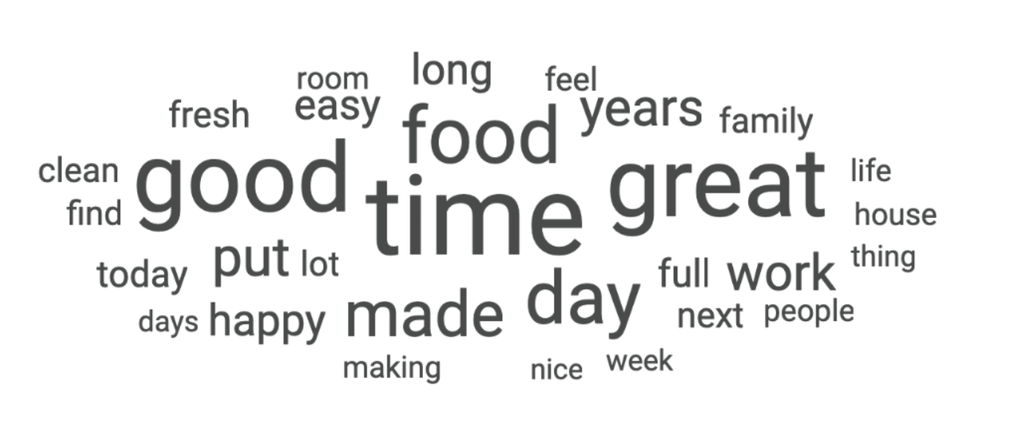
So, what is it about these budget electronics that’s so enticing? We used Brandwatch Consumer Research to pull a word cloud on household devices to see which topics come up regularly.
With over 108k mentions, ‘time’ is a top hit. People are keen to find devices that offer time-saving qualities and will happily leave online reviews or comments for products that help.
‘Easy’ and ‘clean’ are also among the top mentioned words in the household goods conversation, showing that products which help make consumers’ lives easier are always a hit.
Forum-based sites – especially Reddit – can be an excellent place to monitor real-time product reviews and recommendations for budget gadgets. There are subreddits for everything and brands can tap into these conversations to better understand why people are using their products, and under what circumstances.
People are also quick to share their latest purchases online with friends and followers – especially if they’ve found a good deal or are excited about a new find.
Just made the best buy on temu... Will show u guys when it arrives pic.twitter.com/rxNcFYTpMA
— ämpi🛸ia (@glownoos) October 3, 2024
Brands might benefit from tapping into this excitement and sharing mentions from customers who express excitement or happiness after purchasing as a form of ‘social proof’. Whether it’s through generating hype via follow up email marketing, or finding indirect mentions in UGC posted on social media to repost, manufacturing even more excitement about your products can pay off.
Retro tech products are making a comeback
Growing consumer demand for nostalgia is seeping into the tech sector. Retro products are popping up across the consumer technology industry, and brands are seeing plenty of positive feedback about these releases online.
From Nokia’s “Barbie” flip phone to a resurgence of the Tamagotchi phenomenon, consumer tech brands are seeing plenty of success when releasing retro products. In fact, Tamagotchi has even opened its first in-person store in the UK after sales doubled last year.
So, why does retro work? These products elicit strong emotional reactions. Older generations feel nostalgic as they experienced the products when they were originally released first-hand, and younger generations are drawn to their iconic designs, prior renown, and tech simplicity. Tapping into these largely positive emotions can get consumers talking about your brand in favorable ways.
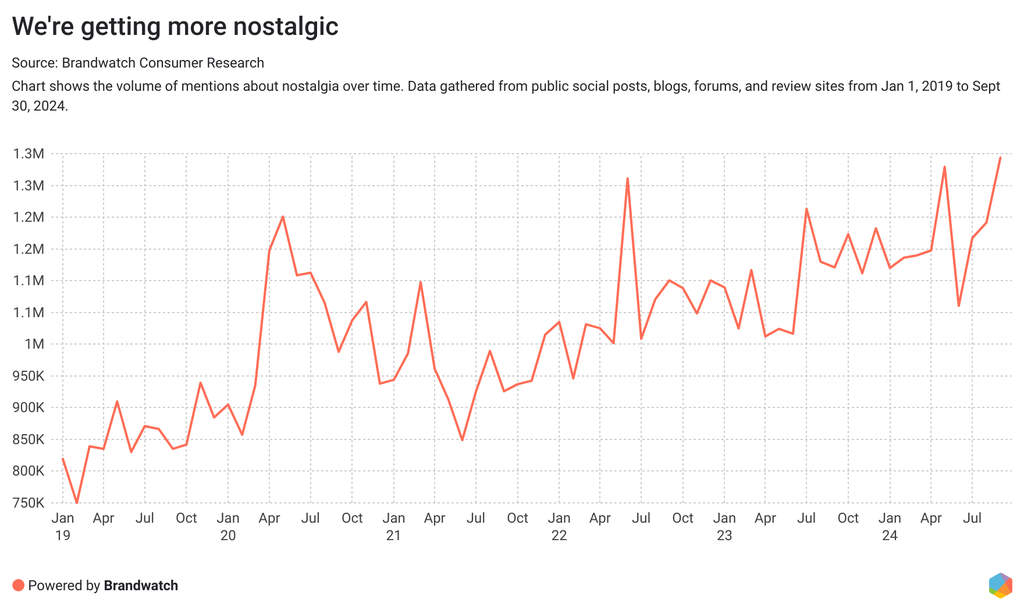
We used Brandwatch Consumer Research to discover how people are talking about nostalgia, and online mentions hit a peak of 1.3 million mentions in September.
These mentions seep into the tech space too. People are increasingly discussing old gadgets, games, and products, hoping to remember simpler times. These conversations are largely positive, with 43% of emotion-categorized mentions expressing joy and 27% expressing sadness – but usually the good kind. For example, feeling sad while longing for old products or memories.
A growing desire to reduce smartphone usage is also a huge factor in the success of retro products. With 40% of Americans aiming to cut down on their screen time, retro tech products are (to some extent) tapping into these desires.
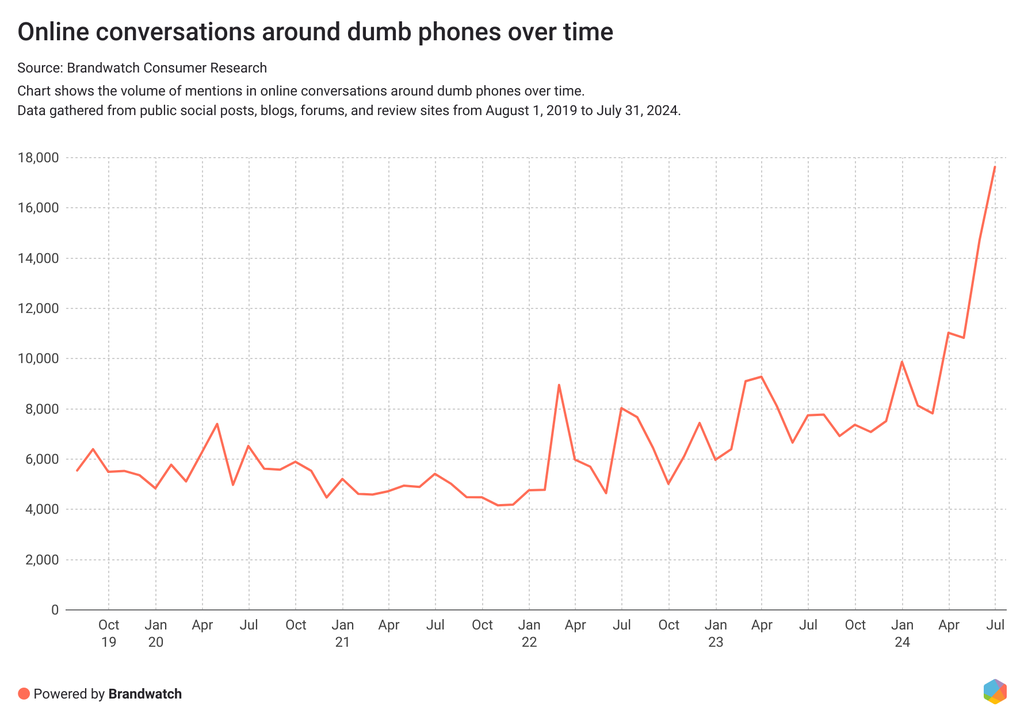
As we discussed in our latest report on health and wellness trends, we’re seeing a growing interest in online conversations about “dumb phones” – or phones which don’t have smartphone features. For example, these phones can make calls and send texts but don’t allow social media apps.
As we can see with “dumb phones”, nostalgia, and the rise of retro, people are leaning into the past – and tech brands should pay close attention to this trend.
Consumers are no longer prioritizing repairs
The number of people opting to repair devices is declining. As electronics become more affordable and disposable income grows, consumers are more inclined to replace than repair broken products.
Whether it’s to prioritize sustainability or to save money, there are a few reasons why consumers might opt to repair over replace. And there’s a consistent conversation about device repairs online. In fact, there have been over 1.72 million mentions about device repairs in the consumer technology conversation between January and October 2024.
Common conversation topics include:
- Consumers looking for recommendations on local repair stores
- People seeking solutions and assistance from support services
- Concerns about costs or elation about finding an affordable fix
- Discussions about hardware defects
- Customer reviews and experiences
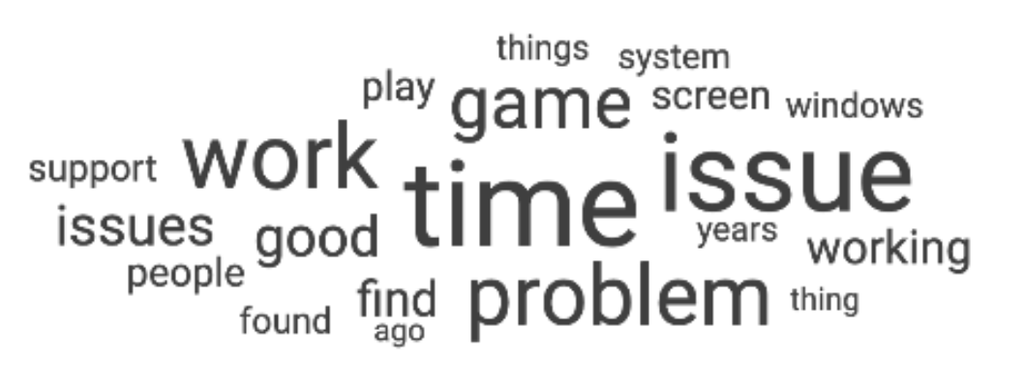
That said, repairing products can come with frustrations from customers. Here’s a word cloud showing the most frequently used words in mentions about repairs. And as you can see, the biggest frustration is time.
Whether it’s the time lost from broken products to the time it takes to get them fixed, downtime is causing upset among tech-reliant customers.
Brands which offer repair services should make the process of getting products fixed as quick and easy as possible. Whether this means hiring couriers to collect broken goods or providing easily-accessible local pick up and drop off points, reducing the time between break and repair is vital for customer satisfaction.
While there’s a downwards trend on fixing devices, buying refurbished tech is on the rise. Confidence in the quality of refurbished tech is improving, and people are opting for cheaper tech options while still expecting brand-new quality.
The number of people that own refurbished products has increased by 70% in the two years running up to 2024. In fact, 14% of smart phones sold over the 2024 holiday period were predicted to be refurbished.
And customers are quick to share their experiences with refurbished products online – especially if they find a good deal.
Lol. I got my PS5 for $300 refurbished :)
— Gerald (@ThatGeralT) August 27, 2024
While just over a third of sentiment-categorized mentioned about refurbished products is positive, 66% of these mentions are negative. These conversations include:
- Challenges with battery issues, faulty components, or poor customer service
- Balancing cost savings with product quality and reliability
- Product durability
So, as repairs take a downturn, the market for refurbished products is growing. But brands need to ensure that a near-perfect standard is met to ensure customers are satisfied.
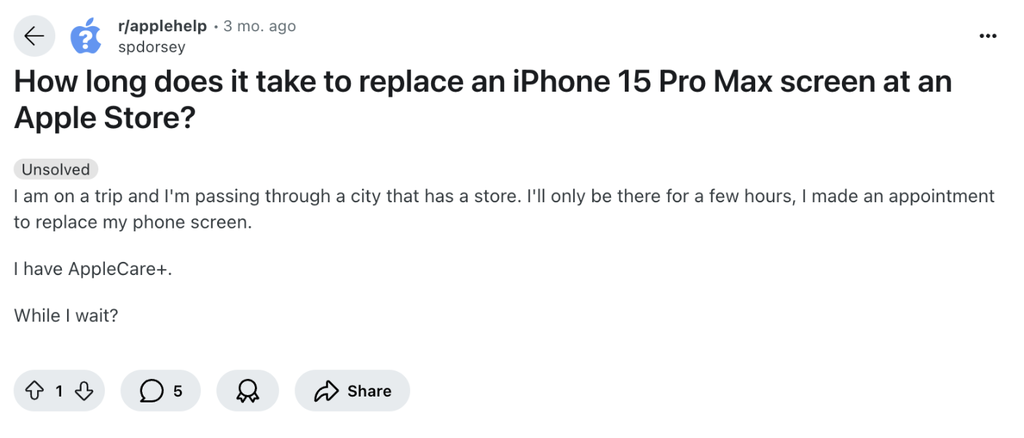
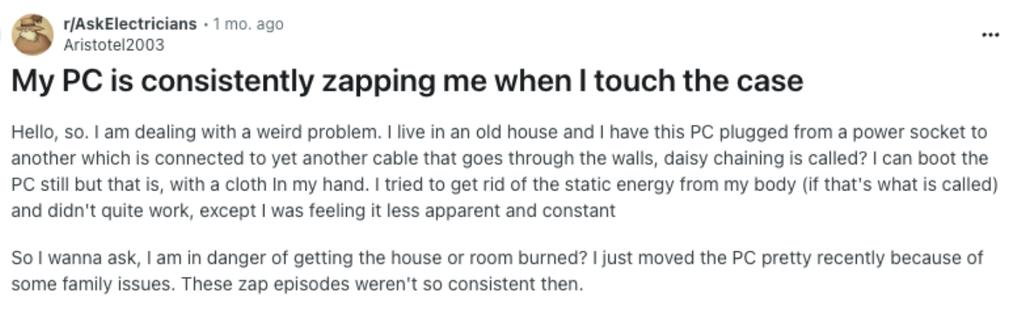
Consumers are peer-diagnosing their tech issues
People are taking to third-party online forums to diagnose their tech issues. Rather than heading to brand websites, which can be hard to navigate, customers are asking questions about device repairs on websites like Reddit.
The most used subreddits for consumer technology peer-diagnosis are r/techsupport, with 17.3k mentions, and r/pcmasterrace, with 12.6k mentions. Other popular subreddits include r/buildapc and r/pchelp.
These forums are jam-packed with helpful information for consumers, which often provide information faster and more directly than a brand’s customer support options or help center. By being aware of these forums, brands can gain valuable information about the problems customers are facing with their consumer technology products.
Wearables are set to boom
The wearables market is only growing. From wireless earbuds to smartwatches and fitness trackers, consumers are excited about how these gadgets can improve their day-to-day lives.
The number of smartwatch users is expected to increase by 62% in the next 5 years, as the demand for functional tech rises. People are spending more on wearables, too, with the average spending per consumer expected to increase by 18% by 2025.
There were over 2.54 million online mentions about wearables between January and October 2024. From headphone preferences to smartwatch insights, consumers are asking for advice on the best wearables to purchase based on their specific needs.
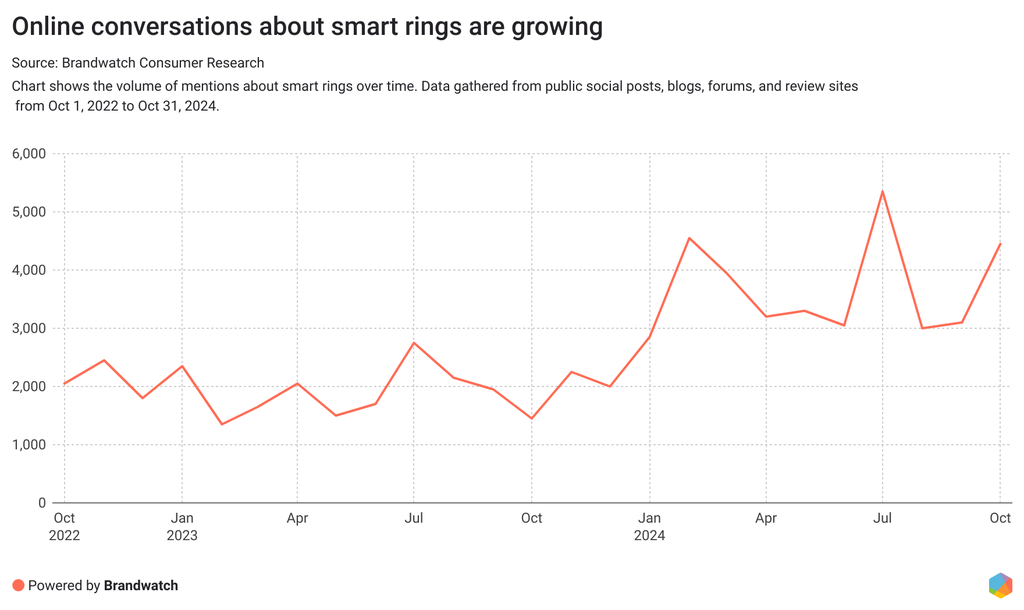
Smart rings are all the rage
There’s also a growing focus on fitness tracking – especially in the form of smart rings. These compact devices work by tracking your heart rate, sleep, and activity.
An added benefit? They blend in. A growing number of consumers are opting for a smart ring over something more traditional, like a watch, due to their subtlety. And online mentions are growing to reflect this.
While watches are helpful and offer more functionality due to their screens and buttons, rings collect data passively – which users can check as they please. Plus smart rings are making people feel better informed about their bodies.
These rings, alongside other fitness trackers, are implementing features that rival hospital treatment – such as checking body temperatures or providing EKGs. Potential consumers are actively seeking these features too, looking for recommendations on which trackers are the most accurate.
As always in the wearables space, the brands which are the most durable and provide the best feature set come out on top. That said, design is also important. With smart rings, the more subtle, the better.
Brands in the wearables space can learn from the growing interest in smart rings – how can you improve your product design to create smaller, sleeker products that offer the best features?
Lessons for brands in consumer tech
- Focus on artificial intelligence – but only if it’s necessary. Customer frustration can develop when AI isn’t up to scratch, so only get involved when your AI offering is ready for a discerning audience. Plus, make sure you’re up front about your privacy policy when asking for customer data to contribute to your AI’s implementation.
- Don’t ignore YouTube. Long-form videos are successful for consumer tech brands. Aim to post four or five times per week, as per industry benchmarks.
- Optimize your customer support and help centers. Make sure your self-hosted online forums for customer support are efficient. Utilize third-party forums like subreddits to study and address customer pain points.
- You don’t need to stand out from the crowd. The boom in smart rings and subtle wearables proves that sometimes blending in is better. See if you can make your products smaller, sleeker, and more attractive.
- Follow the trends. There are huge opportunities for tech brands looking to move fast on trends like nostalgia and must-have gadget categories. Tracking online mentions of the tech space can help you make smart decisions at pace.